Electronic signature: legal value, eIDAS levels and risks
Since joining Polytech Services Nancy, we have signed hundreds of documents electronically: project agreements, expense reports, membership forms, and more. But a question quickly nagged at me: do these signatures carry the same legal weight as a handwritten signature on a sheet of paper?
The answer is far from straightforward. It led me to dig deep into the subject, to the point of running a training session on the different types of electronic signatures. Compliance with the legal and regulatory framework is indeed a core component of the code of ethics that governs Junior-Enterprises belonging to the CNJE — which means we simply cannot afford to sign just anything, any which way.
As always, I want to be clear upfront: I receive no compensation whatsoever for writing this article. The opinions expressed here are based solely on my personal experience within the association.
With that disclaimer out of the way, let’s get into it. Here is what I’ve taken away from the experience.
Electronic certificate: definition and role in digital signatures
Before talking about signature levels, it’s essential to understand the underlying mechanism. An electronic signature relies on asymmetric cryptography : the signer holds a private key (secret, known only to them) and a public key (shareable). When they sign a document, they compute a digital fingerprint (a hash) of it, which they encrypt with their private key. Anyone can then verify this signature using the public key: if the fingerprints match, the document has not been altered and the signer is authenticated.
But how can one be sure that the public key actually belongs to the person it claims to represent? That’s where the electronic certificate comes in: an identity attestation issued by a Certificate Authority , which guarantees the link between a public key and its holder’s identity — name, pseudonym, registration number, etc.
This certificate may be qualified or not. A qualified certificate is issued by a provider subject to strict controls, audited by a competent and independent third party, and listed on a Trusted List published by each EU Member State. In France, it is the ANSSI (National Agency for the Security of Information Systems) that oversees this list.
Electronic signature vs. electronic seal: don’t mix them up
The European regulation eIDAS (No. 910/2014) draws a distinction between two concepts that are often conflated, and this distinction is fundamental in a Junior-Enterprise context.
An electronic signature is performed by a natural person. It expresses the signer’s consent, much like a handwritten signature. This is what the president of a Junior-Enterprise uses to sign a project agreement.
An electronic seal is issued by a legal entity — a company, an association. It does not constitute personal consent; it attests that the document originates from the organisation and guarantees its integrity. It is the digital equivalent of a company stamp.
This distinction matters greatly in practice. Many mainstream solutions actually apply an editor’s seal to the document rather than a user signature. For the actual signer, the effective signature level may be far lower than what the platform’s interface implies. We’ll come back to this.
The four eIDAS signature levels
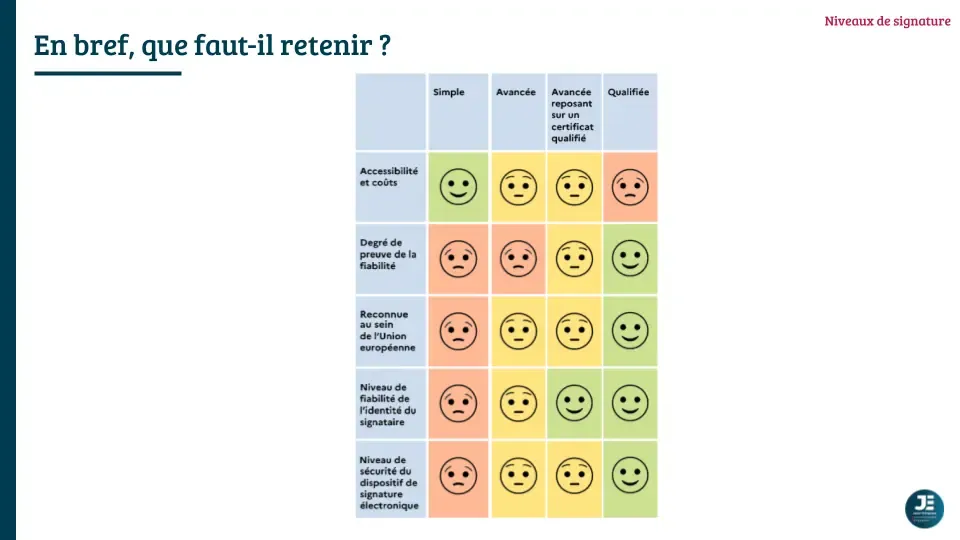
The eIDAS regulation defines four levels of electronic signature, from the most accessible to the most robust.
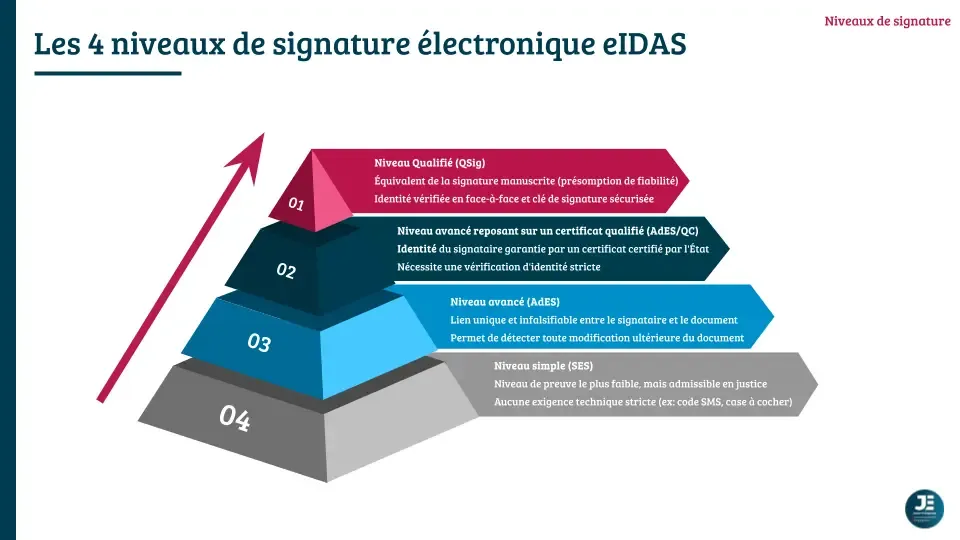
Level 1 — Simple Electronic Signature (SES)
This is the minimal definition: electronic data associated with other data and used by the signer to sign. A code received by SMS, a checkbox, a signature sketched on a tablet — all of these can constitute an SES.
No precise technical requirements are formalised and the signer’s identity is not guaranteed. In the event of a dispute, a body of evidence must be assembled (timestamp, data integrity, assumed identity). A judge cannot reject an SES solely on the grounds that it is electronic, but the burden of proof falls entirely on the signer.
In this case, LiveConsent compensates for this level by producing a completion certificate — a set of contextual evidence (timestamp, IP address, SMS or email validation) that can be presented in the event of a dispute. This is the classic mechanism of a well-documented SES, but it is not a cryptographic signature from the user.
Level 2 — Advanced Electronic Signature (AdES)
The advanced signature meets specific requirements formalised in the regulation: it is uniquely linked to the signer, allows them to be identified, is created using data under their sole control, and allows any subsequent modification of the document to be detected. It must be accepted by the public bodies of Member States that use this level.
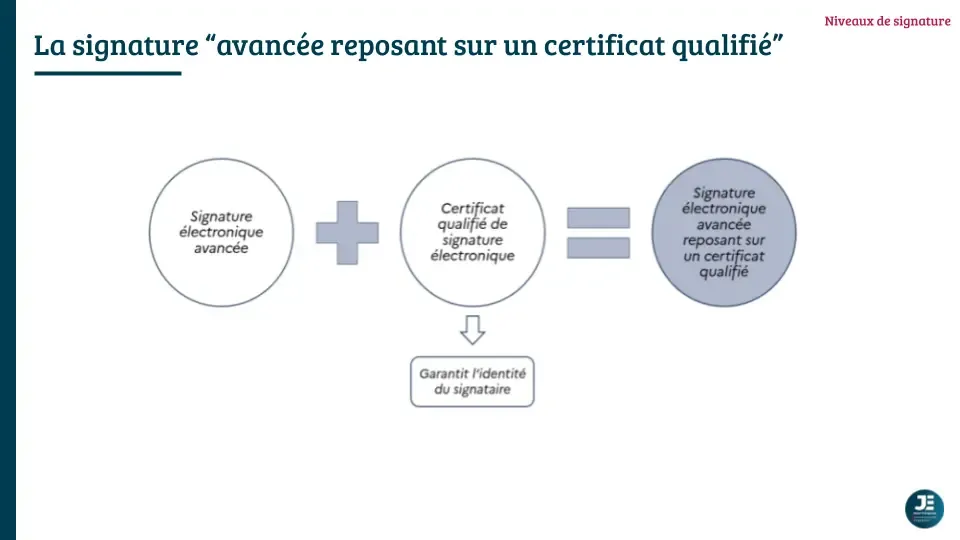
Level 3 — Advanced Signature Based on a Qualified Certificate (AdES/QC)
Here, the qualified certificate comes into play. In addition to the properties of the advanced signature, the signer’s identity is guaranteed by a provider audited and overseen by the ANSSI. Identity verification can be carried out in person with a qualified agent, remotely via a certified service (PVID framework), or through a previously established electronic identity (such as France Identité). The evidentiary burden is considerably eased in the event of a dispute. This level is mandatory for public procurement (ministerial order of 22 March 2019).
Level 4 — Qualified Electronic Signature (QESig)
The highest level. It combines the advanced signature on a qualified certificate with a Qualified Electronic Signature Creation Device (QSCD): a certified smart card, an authentication key, or a cryptographic hardware device hosted by the provider.
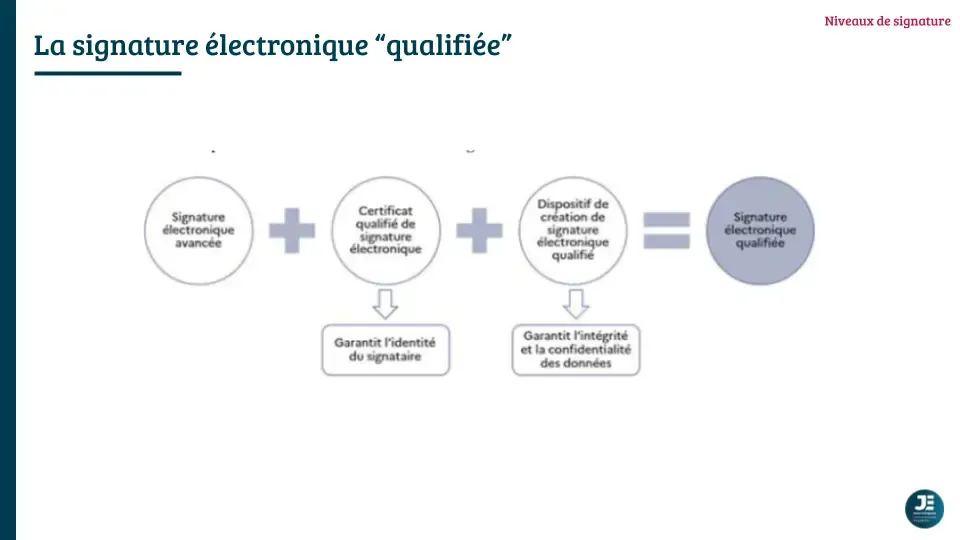
In France, this level enjoys a presumption of reliability: the burden of proof is reversed. It is no longer up to the signer to prove the validity of their signature, but up to whoever contests it to demonstrate a defect. It is legally equivalent to a handwritten signature (Article 1367 of the Civil Code) and recognised in all Member States of the European Union.
Electronic signatures: hidden risks of popular solutions
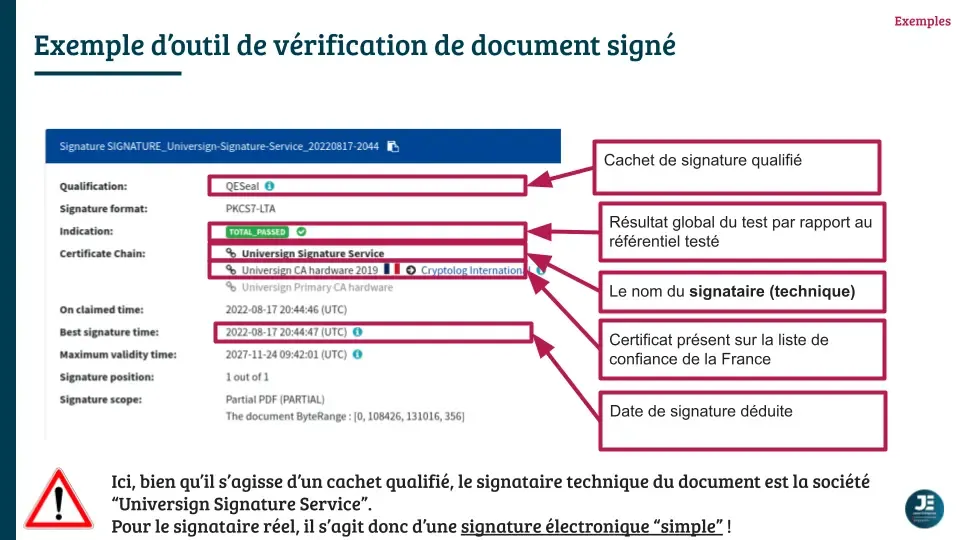
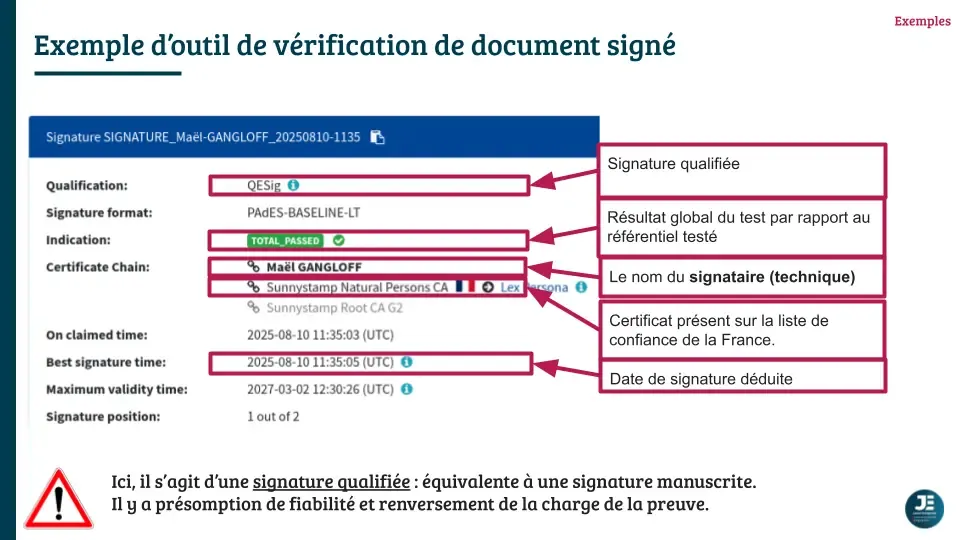
This is the point that surprised me most when I was researching the CNJE training. By using the DSS (Digital Signature Service) verification tool from the European Commission — the reference tool for analysing electronic signatures — one can examine precisely what a document actually contains.
With LiveConsent, the solution we used at Polytech Services Nancy, here is what the tool reveals: the qualification returned by DSS is AdESeal-QC (advanced seal based on a qualified certificate), with “LiveConsent” in the certification chain. This is not the user’s signature — it is the provider’s seal. For the person who clicked “I sign”, this amounts to a simple signature (SES), regardless of the level displayed in the platform’s interface.
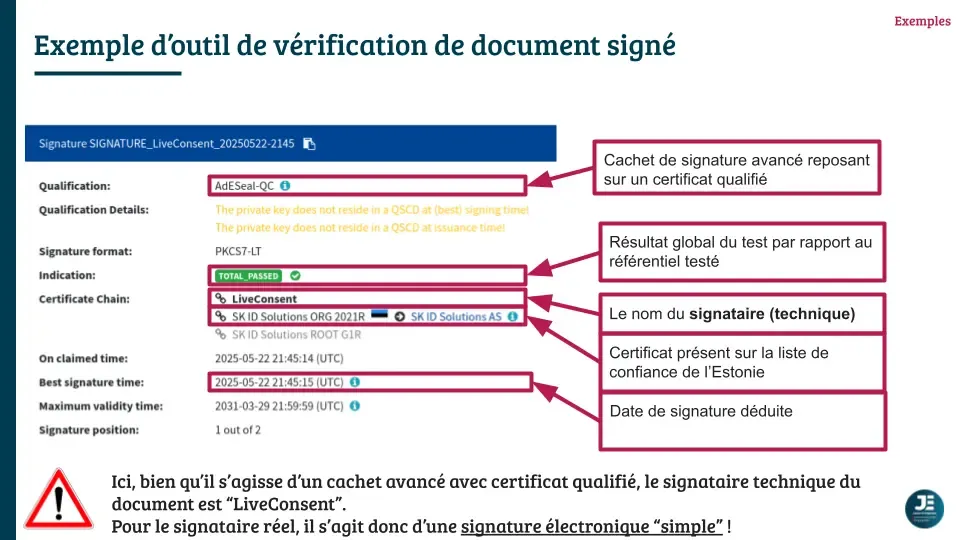
The same finding applies to other popular solutions: DSS sometimes returns a qualified seal from the software publisher, not a user signature.
This is not necessarily a problem for low-stakes internal documents, for which an SES is perfectly adequate. But it is essential to know what you are actually using, especially when contractually committing a Junior-Enterprise.
How to verify a signed document
Two main tools allow you to verify the quality of an electronic signature.
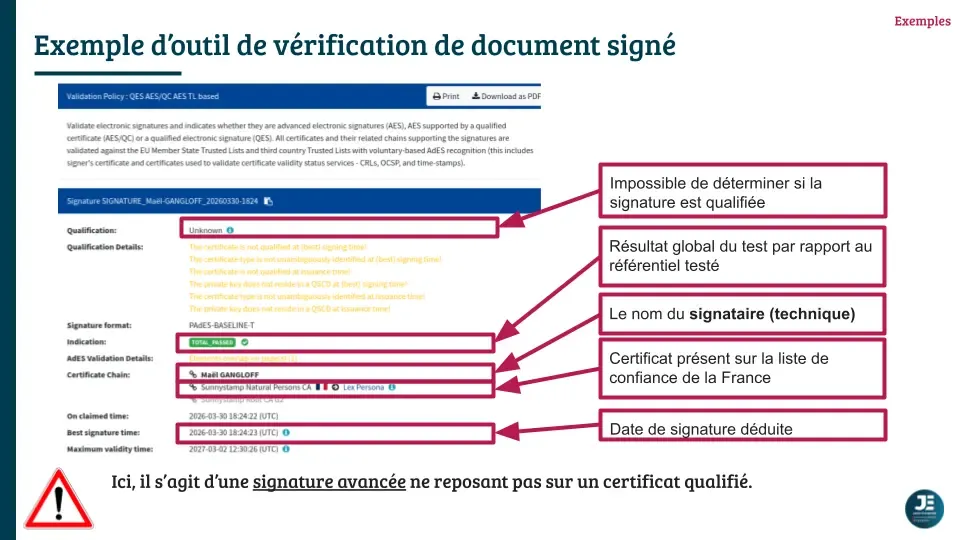
The European Commission’s DSS validator is the reference tool, free and publicly available. It indicates the qualification of each signature present in the document (QESig, AdES/QC, AdESeal-QC, etc.), the timestamp, the certification chain, and whether the certificate appears on a national Trusted List.
Adobe Acrobat Reader also allows you to view electronic signatures in a PDF and verify their validity, provided that the certificates are recognised by Adobe.
For Junior-Enterprise use, I recommend running important documents through the DSS validator. The interface is clear and the information returned lets you know exactly which signature level you are dealing with.
Our switch to Goodflag Community (Lex Persona)
Following the training session and this realisation, we decided at Polytech Services Nancy to evolve our practices. We now use the free solution provided by Lex Persona for documents requiring an advanced signature.
The difference is fundamental: with Goodflag Community, it is indeed the signer who applies an advanced electronic signature (AdES) to the document — not a provider seal. The certification chain belongs to the user, and the DSS validator confirms this clearly.
It is also possible to opt for a qualified electronic signature through this provider’s interface. However, at this stage, the signer must have the government application France Identité in order to sign at this qualification level.
In summary: how to choose the right level?
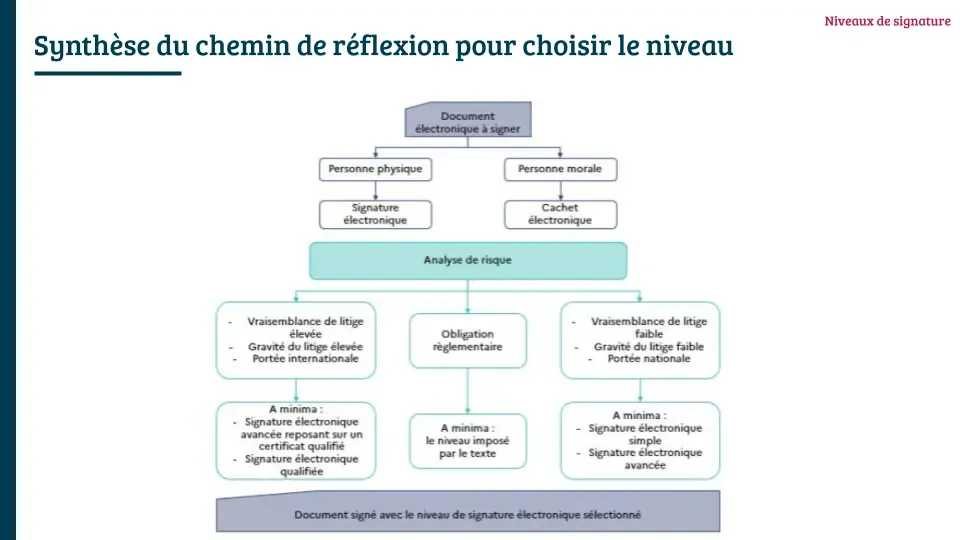
The decision framework recommended by the ANSSI in its selection guide is based on a risk analysis across five factors: the scope of the document, applicable regulatory requirements, the likelihood of a dispute, the severity of such a dispute, and the type of document.

For a Junior-Enterprise, here is a practical grid of my recommendations:
| Document | Minimum recommended level |
|---|---|
| Board meeting minutes | SES |
| Client / contractor project agreement | AdES |
| Treasury document, certificate | AdES |
| General Assembly minutes | AdES |
| Public procurement tender | QESig (legal requirement) |
| High-stakes financial project document | AdES/QC or QESig |
The higher the likelihood and severity of a potential dispute, the more advisable it is to choose a level offering strong evidentiary value. And for documents with European reach, a qualified signature is mandatory — it alone benefits from mutual recognition across all EU Member States.
A different approach in Europe: the Belgian case
It is worth noting that not all EU Member States have made the same choices regarding digital identity and electronic signatures. Unlike France, Belgium provides all of its citizens with an electronic identity card (eID) that directly integrates a qualified digital certificate. In practice, this means that every Belgian citizen, upon receiving their card, already has the means to produce qualified electronic signatures and to authenticate online with a high level of assurance, simply by using a smart card reader.
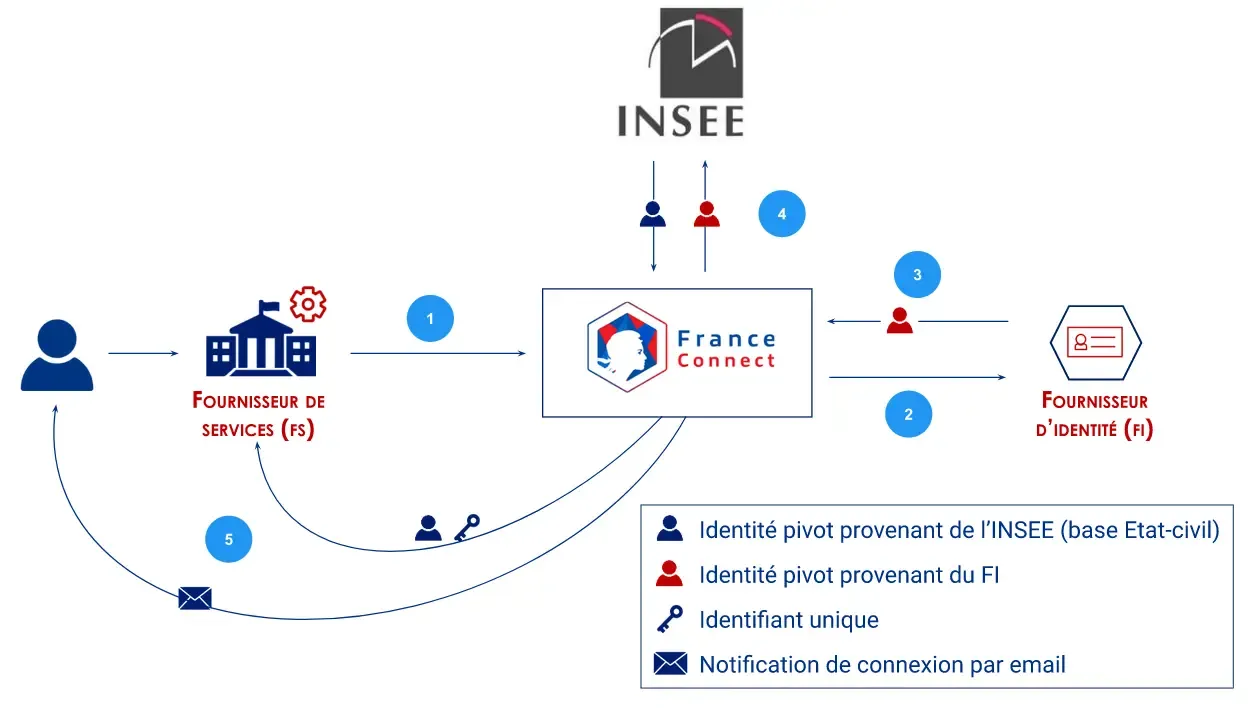
This approach is built on a decentralised infrastructure: proof of identity and signing capability are carried on a physical medium held by the user. By contrast, for online authentication, France opted for FranceConnect, a state-managed, centralised solution that aggregates several identity providers (tax authority, Ameli, etc.). This model has advantages in terms of ease of use and integration, but also carries the classic limitations of centralised systems (single point of dependency, governance concerns, larger attack surface).
On the electronic signature side, the contrast is even starker: to date, France does not offer a universal and free service allowing every citizen to easily exercise their right to a qualified electronic signature, unlike other European countries such as Belgium, where this capability is natively embedded in the national identity infrastructure.
Conclusion
The electronic signature is a powerful tool, but its legal value depends entirely on the level at which it is executed. Many mainstream solutions do not make this reality transparent. As a member of a Junior-Enterprise committed to upholding the CNJE’s legal and ethical framework, understanding these distinctions is, in my view, indispensable — and routinely underestimated.
The eIDAS regulation provides a solid, harmonised framework at the European level. The tools to verify and choose the right signature level exist and are often freely available. All that remains is to make use of them.
Want to learn more about my Junior-Enterprise journey? Read my article on my experience at Polytech Services Nancy.
Disclaimer
This article is published for informational and educational purposes only. I am not a lawyer, attorney, or expert in digital law.
The information presented reflects a personal analysis of the regulatory texts in force at the time of writing, including the eIDAS Regulation (No. 910/2014), the French Civil Code, and the decree of March 22, 2019.
This information does not constitute legal advice and should not be considered a substitute for the opinion of a qualified legal professional. For any questions regarding the legal validity of an electronically signed document in your specific situation, it is recommended that you consult a lawyer or a specialized legal expert.
As regulations regarding electronic signatures are subject to change — particularly with the rollout of eIDAS 2.0 and the development of France Identité — I do not guarantee the accuracy, completeness, or timeliness of the information beyond the publication date of this article.
FAQ
What is the difference between an electronic signature and an electronic seal?
An electronic signature is issued by a natural person and attests to their consent. An electronic seal is issued by a legal entity (company, association) and attests to the integrity and origin of the document, like a digital stamp. Many mainstream platforms actually apply an editor’s seal rather than a genuine user signature.
Does my signature via LiveConsent have legal value?
It depends on the document and the context. For low-stakes internal documents, a simple signature (SES) is generally sufficient. For significant contractual commitments or public procurement, a higher level (AdES/QC or QESig) is required. Use the European Commission’s DSS validator to find out the actual level of a signed document.
How do I obtain a genuine advanced or qualified signature?
For an advanced signature (AdES), solutions such as Lex Persona offer a free tier. For a qualified signature (QESig), you must go through a provider listed on the national Trusted List and obtain a qualified certificate, which requires identity verification (in-person, certified remote service, or via France Identité). The list of qualified providers in France is available on the ANSSI website.
What signature level is required for public procurement?
The ministerial order of 22 March 2019 on electronic signatures in public procurement mandates a qualified electronic signature (QESig).
How do I verify an electronic signature on a PDF document?
Two main tools: the European Commission’s DSS validator (free, official reference) and Adobe Acrobat Reader (for PDFs with embedded signatures recognised by Adobe). The DSS validator is the most comprehensive: it indicates the exact qualification, the certification chain, and whether the certificate appears on national trusted lists.
